Portable Expert System for the Secure and Semi-Automatic Acquisition of Digital Evidence
Celia CatalánShare
.jpg)
Today we present you an analysis, perhaps too light, of a current problem for which we propose a solution that is probably not so light.
Where we are?
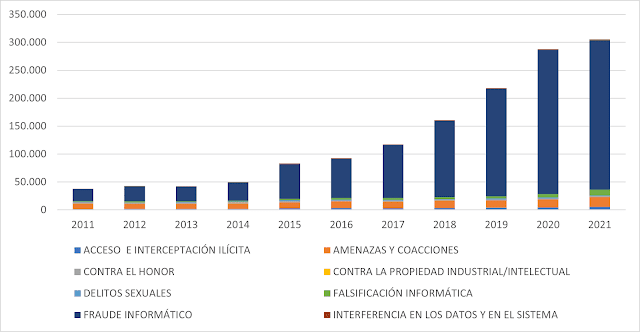
According to the Criminal Statistical Portal of the Ministry of the Interior of Spain, the number of known facts related to cybercrimes has not stopped increasing since 2011. The criminal group that is growing the most, and that has the greatest incidence, is computer fraud, which the Spanish Penal Code defines as the crime of fraud through the illicit manipulation of data and/or programs for profit.
Furthermore, currently, not only the crimes classified as cybercrimes have a technological component in which it is necessary to carry out some investigation on some digital medium such as a mobile phone, a laptop or a server.
On the other hand, the number of clarified facts is much lower than the known ones and its growth trend is not close to that of the former:
Therefore, the number of cases in which the help of computer forensic analysis is necessary within a judicial process is increasing.
But in reality the existence of litigation is not necessary for it to be advisable to carry out a forensic study of a computer infrastructure. Many companies, internally, use forensic analysis methodologies to resolve, prevent, reduce and control the occurrence of fraud within the organization. Samples or evidence are often taken for future use in possible internal control or judicial processes.
Almost all forensic analysis methodologies summarize their operations in the well-known five phases that we allow ourselves to remember:
1st Acquisition. Where a copy of the information that can be presented as evidence in a process is made. This evidence must be collected without altering the originals, using read-only devices or procedures that guarantee that the source storage medium is not overwritten. The volatility of the samples must be respected and their collection prioritized. And all original devices must be labeled and stored securely.
2nd Preservation. In this phase, the durability over time and the chain of custody of the information collected are guaranteed.
3rd Analysis. Techniques are used that, together with the experience and intelligence of the analyst, will help resolve the what, how and who of the case analyzed.
4º Documentation. Phase in which it is ensured that the entire process (information and procedures applied) is correctly documented and dated.
5th Presentation. Where at least one executive report and another technical report are generated, collecting the conclusions of the entire analysis.
Judges take into account how digital evidence is collected and stored, its validity depending on the methods chosen. Therefore, it is evident that the acquisition and preservation phases are fundamental to the entire process. If any errors are made in these phases, all research, together with all subsequent analyses, will no longer be valid.
What is the problem?
In Electronic evidence - A basic guide for First Responders - ENISA proposes the following principles that must be ensured in the management of digital evidence:
- Data integrity. No data that must be used in the resolution of a case by a court should be modified. The person in charge of the crime scene or collection is responsible for ensuring that this does not happen. Additionally, if the device picked up is turned on, the acquisition should be done in a way that modifies it as little as possible.
- Registry. A record must be created and updated with all the actions carried out on the evidence collected, from its acquisition to any subsequent consultation.
- Specialist support. At any time during the acquisition, the intervention of a specialist duly trained in digital forensic techniques should be possible. Said specialist must have sufficient technical and legal knowledge, as well as the necessary experience and authorization.
- Training. Anyone who handles digital evidence must have basic technical and legal training.
- Legality. The corresponding legality must be ensured throughout the entire process.
Always with these principles in mind, in the acquisition phase you have to make decisions and answer complicated questions such as:
- Where is the information physically located?
- Which storage devices to copy.
- Should a device be turned off to perform the acquisition?
- Order to make copies, taking into account the volatility of the data involved.
- Is it necessary to search for and copy hidden, non-visible or remote devices?
- Have anti-forensic techniques been used to hide information?
- Need for support from a forensic specialist.
- Need for a notary.
Various profiles of professionals with different levels of responsibility, training and experience may occur at the crime scene. Not all of them can successfully answer the above questions.
Clearly, the number of appropriately qualified professionals to carry out these forensic acquisitions is not sufficient. Other factors that complicate the situation are movement restrictions, teleworking, the need to operate in hostile environments or budget limits.
In this scenario, an autonomous and portable system would be of great help, which could be operated by a person without specific training, to assist in the secure acquisition, storage and documentation of digital evidence.
What we have?
There are multiple specific tools on the market for acquiring evidence. Some are commercial and others are free to use. Below, we leave you a list with some of the most representative and used ones, comparing their main characteristics:
They all have in common that they are complex to use, that they require specific training for their use and, above all, that they can be dangerous if not used correctly, it is easy to incur irrecoverable data loss.
On the other hand, there are many Linux distributions aimed at computer forensics that provide specific tools for acquiring evidence. Among all, we highlight the following due to their degree of updating and specialization in the forensic process:
We all know that there are other very complete distributions that cover not only the forensic analysis process but any area related to cybersecurity. Among them it is worth highlighting Kali Linux, BlackArch Linux, Matriux, BackBox Linux or Parrot.
All of them have the best tools for forensic analysis and with all of them it is possible to securely acquire digital evidence. All of them have undoubted value for the cybersecurity professional. But in the context of this analysis, they all have some drawbacks:
- They can be complex to implement if you do not have sufficient knowledge.
- They need specific technical training to use their forensic tools.
- They are not designed specifically for the acquisition of digital evidence.
What do we propose?
A system that makes it possible to eliminate all these deficiencies, offering a specific solution for the acquisition of digital evidence, which allows an operator without much knowledge to collect, safely and anywhere, data and information that could be used in a judicial process.
Below, we allow ourselves to imagine a list of characteristics desirable during the acquisition, preservation and documentation phases and not found together in any of the previous distributions:
- Portable, dedicated and self-contained integrated system.
- Intuitive user interface, simple and easy to use, requiring almost no learning.
- User interface that avoids or minimizes errors due to ignorance or malicious intent.
- Guidance of activities for inexperienced users through an expert system that implements the intelligence and experience of a forensic analyst.
- Helps in identifying evidence. Often little or not visible at all.
- Secure acquisition (in integrity and availability) of storage devices.
- Use of the correct technique according to the type of evidence.
- Assistance in physical storage and labeling of acquisitions.
- Configuration of the chain of custody of digital evidence.
- Generation of activity log.
- Generation of documentation.
Furthermore, we could imagine that it integrated utility functions in the analysis and presentation phases of the forensic process, thus being able to cover the entire forensic process. Even add specific intelligence for the analysis of new cases of fraud, industry and IoT, critical infrastructures, etc.
Let's imagine a generic use case:
Or the general flow of our system:
Let's imagine the necessary data model:
Or even what its interface could be like:
Concluding
There are all the system design, implementation and integration tools necessary to develop a system like the one we have now imagined. It is possible to develop an expert system that helps personnel without specific training in computer forensics to carry out a guided and safe acquisition of the evidence necessary to resolve a security incident.
It is possible to integrate specific techniques, procedures and tools with an expert system that implements the intelligence of a forensic analyst in software that can be used by users with little knowledge in an environment that requires very exhaustive methodology, integrity and documentation.
Immediate response teams such as security forces, junior forensic experts and IT and communications professionals could be its main users. The principles of security and integrity under which it would be developed would allow its use in investigations and judicial procedures or in internal audits within private or public organizations.
We hope this article has served as inspiration to many. Imagining and dreaming is free and some even make it come true. If you are one of those join us.
Iván Paniagua Barrilero, Teachnical Lead at Zerolynx.